The phrase “I just got hacked” is something commonly said by people who got their virtual accounts compromised. Here’s the thing, hackers are not people who just saw or heard your password then went on accessing your account, these people are simply called observant and very stalker-ish.. hahaha!
Real HACKERS, on the other hand, are on a different playing field. They observe the flow of data from one computer to another, fully understanding binary communication. There are many security measures to prevent an attack from these individuals. But before we talk about protection, we should first classify different types of hackers.
Hackers – In General
Hackers are people who are extremely knowledgeable about computers and how the Internet works. They have honed themselves to play inside the world wide web like playing the highest level of TETRIS.
It takes a lot of time and effort to understand how bits of information are stored into packets and transferred through the web or a network with the use of different ports from server to server. It is not an easy feat because transmission of data happens to be very fast like a couple of milliseconds or so. This is of course depending on the speed of your computer and Internet Service Provider.
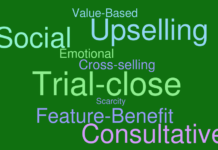
White–hat Hackers:

They are the good guys that mastered the “ETHICAL” ways of hacking and are experts at their own playing field. They use their abilities for good, ethical, and legal purposes rather than bad, unethical, and criminal reasons.
Here’s an example, let’s just say you have an organization or a company that would like to protect from virtual attacks. More often than not, you would want to think about hiring a White-hat Hacker to ensure that your server is protected from malicious attacks. Think of them as goalkeepers. 🙂
Note: It is not easy to be a white-hat hacker as it is always easier to break than to build.
Black-hat Hackers:

Of course if there’s white, there has to be black. Sometimes called “crackers”. Plain and simple, they are individuals who went to the dark side to find ways on how to make people miserable or to steal from others.
They can break into someone’s computer system (often on a network); bypasses password or licenses in computer programs, or intentionally breaches computer security.
Funny enough, some black-hat hackers often start by creating a virus and releasing it on their own computer which fries their system. Then if they’re up to it, they’ll release this to the general public so that they can gather information from computers around the globe or simply to make others suffer.
Why are there black-hat hackers? Other than trying to steal, the true reason there are is that they find it exciting. They find joy in tapping into your personal computer or virtual account, for the purpose of using illegally gathered information as leverage against you.
Protection

There are actually a lot of ways to protect yourself from hackers, below are common practices and some good-to-know information that I’d like to share.
Update your system regularly or even automatically.
Why? Of course, a hacker would first need to know how the system works. To do so, they need to gather data from a dummy system then try penetrating it simultaneously.
Hackers set-up their own virtual private server. Install commonly used program (the one that they would like to penetrate) then try cracking it.
If you update your system regularly, black-hat hackers might not cope up with the frequent change in security measures.
Use an Anti-Virus program
To be safe, you would need to find a good and trusted antivirus program. Personally, I use Windows Defender because it came with the package and I think it has noble intents. Update it regularly though.
Avoid storing very sensitive data in your computer
like passwords, nude pics (lol), bank account information, credit card information, and the like. This is self explanatory (specially IF you are not sure that your computer is 100% secure).
Passwords
For earth’s sake, change your passwords regularly, every 3 months would do. Use 8 characters with at least one capitalized letter, one number, and one special character. Something like iLoveListseed.com143++ would be very very secure… and flattering. haha!
Purchasing via Internet (Very Important )
Check your browser bar before entering your credit card information or any sensitive information. The URL on the browser bar should have HTTPS on it. This means that there is an added encryption to the transmitted data. for example https://www.listseed.com. Now what’s the difference between HTTP & HTTPS?
HTTP: It means HyperText Transfer Protocol.
A protocol used to access the internet through port 80, Imagine your data riding in a PUBLIC bus with other people snooping around or talking to each other.
In a public bus someone has the ability snatch your purse or even punch you if you’re not careful. So yeah, someone can steal your information.
HTTPS: The “S” stands for Secure, companies/individuals that have this on their website took the extra mile for their audience by setting up a product called SSL (Secure Sockets Layer).
SSL is an additional layer of protection in which data packets passes through port 443, it ENCRYPTS all the data being transferred from your computer to the destination server.
Let’s just say you wanted to buy something online and entered your credit card information 12345, on the way to the server, other people in the web would see garbled texts like SxD1#ud+mxCd1A2%@#aa instead of 12345. – If SSL is installed.
This makes it very hard for hackers to crack. When information enters the destination server, it would then be DECRYPTED then your information will be safely transmitted to your trusted retailer.
Be careful of PHISHING attempts
At times we receive email notifications saying that you won a raffle and/or something has been charged to your credit card. THEN it advises you to visit a link or download an attachment to claim the prize / rectify the charge on your card. If you’re in doubt ignore the instructions specified in the mail and delete it, once deleted it is best to block the email sender.
If you are persuaded to click a link or download some content, a virus might spread and compromise your computer. Some viruses will look for sensitive data on your computer and send it to the hacker. If accidentally clicked do these steps:
- Plug off your internet connection.
- Block all ports on firewall settings.
- Run your antivirus locally.
- Change all local passwords, use an UN-compromised computer for changing web related passwords to be safe.
- Backup and delete any sensitive data.
- If credit card is saved on your computer or email, inform your bank for potential fraud. Better yet temporarily deactivate your card. Think twice or thrice before opening peculiar attachments or email links.
Researching if the doubtful email you received has been experienced by other people can help you prevent future attacks.
Please share to spread awareness.












[…] What are HACKERS and How to Protect Yourself? […]
[…] What are HACKERS and How to Protect Yourself? […]